Page History
| Created date | Updated date | Affects version | Fix version |
|---|---|---|---|
|
| Management Portal | N/A |
| Table of Contents |
|---|
Description
Single sign-on simplifies the login process, enhances security and improves the overall user experience. This page introduces the single sign-on feature available in the Blancco Management Portal. Also set of instructions is available to configure and enable SSO for Microsoft Entra ID (Azure AD).
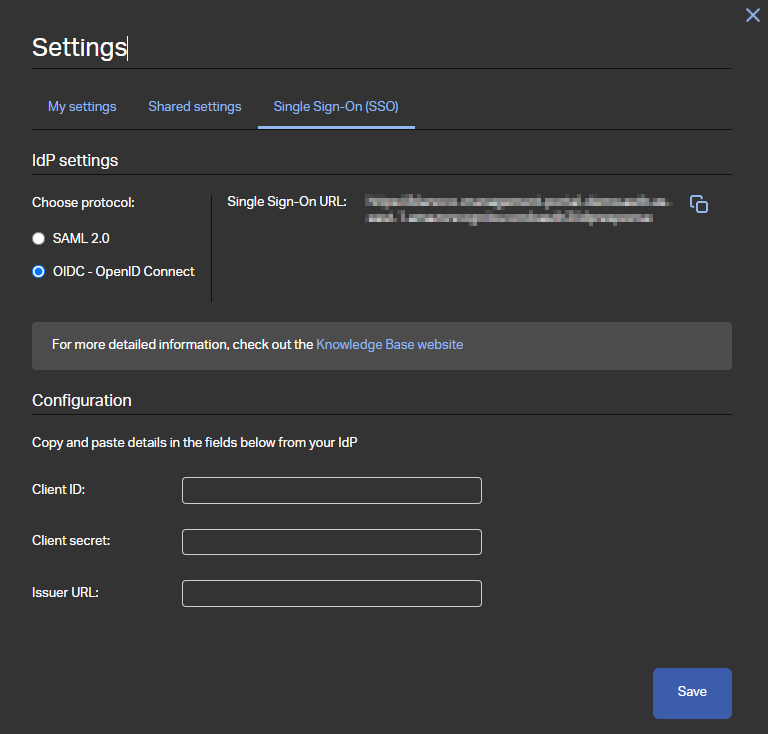
In Blancco Management Portal Single sign-on settings are available for manager users or user with a custom role granting "Configure SSO" authority. SSO settings are available under user's "Settings" which can be accessed by clicking your username from the top right corner of the screen.
...
| Info |
|---|
Single sign-on in Blancco Management Portal also supports user provisioning. This allows Blancco Management Portal to create user automatically to the corresponding tenant when they initially authenticate using single sign-on. |
| Info |
|---|
Note that single sign-on is not supported with Blancco erasure products such as Blancco Drive Eraser or Blancco Mobile Diagnostics and Erasure. Communication between an erasure client and Management Portal requires an internal password of the account to be used. Single sign-on is only supported when logging in to the Management Portal at https://portal.blancco.cloud |
Settings available for SAML 2.0
...
Settings available for OpenID Connect
- Single Sign-On URL - This URL is used as the reply/redirect URL when configuring the SSO settings on the identity provider side.
- Client ID - Application/Client ID of the identity provider.
- Client secret - A string based key used as the authentication technique.
- Issuer URL - Similar to https://login.microsoftonline.com/GUID/v2.0 where GUID corresponds to Entra/Azure tenant ID.
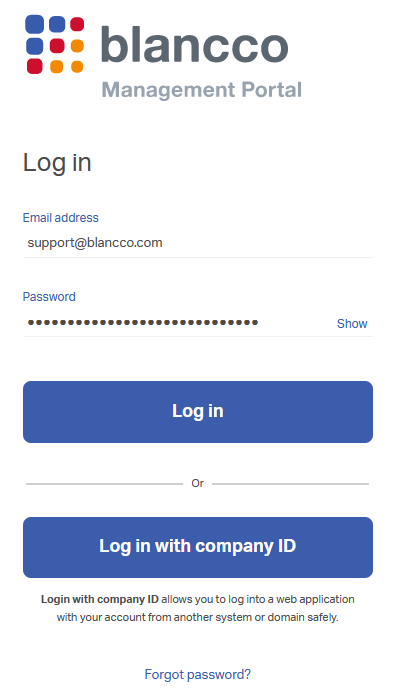
Log in using Single Sign-On
After single sign-on is configured and available for the user, "Log in with company ID" button appears on the Management Portal login screen.
If no email address is provided or the user account in question doesn't have SSO configured this button is not available.
Using the "Log in" button authenticates the user using the internal password of the account and not through the single sign-on.
Microsoft Entra ID/Azure AD - SSO with SAML 2.0
Follow these steps to set up single sign-on with Azure AD using SAML 2.0.
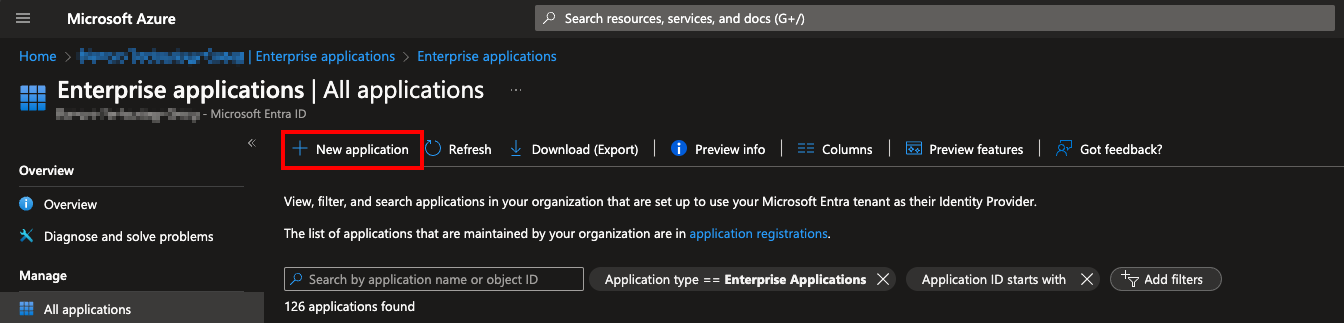
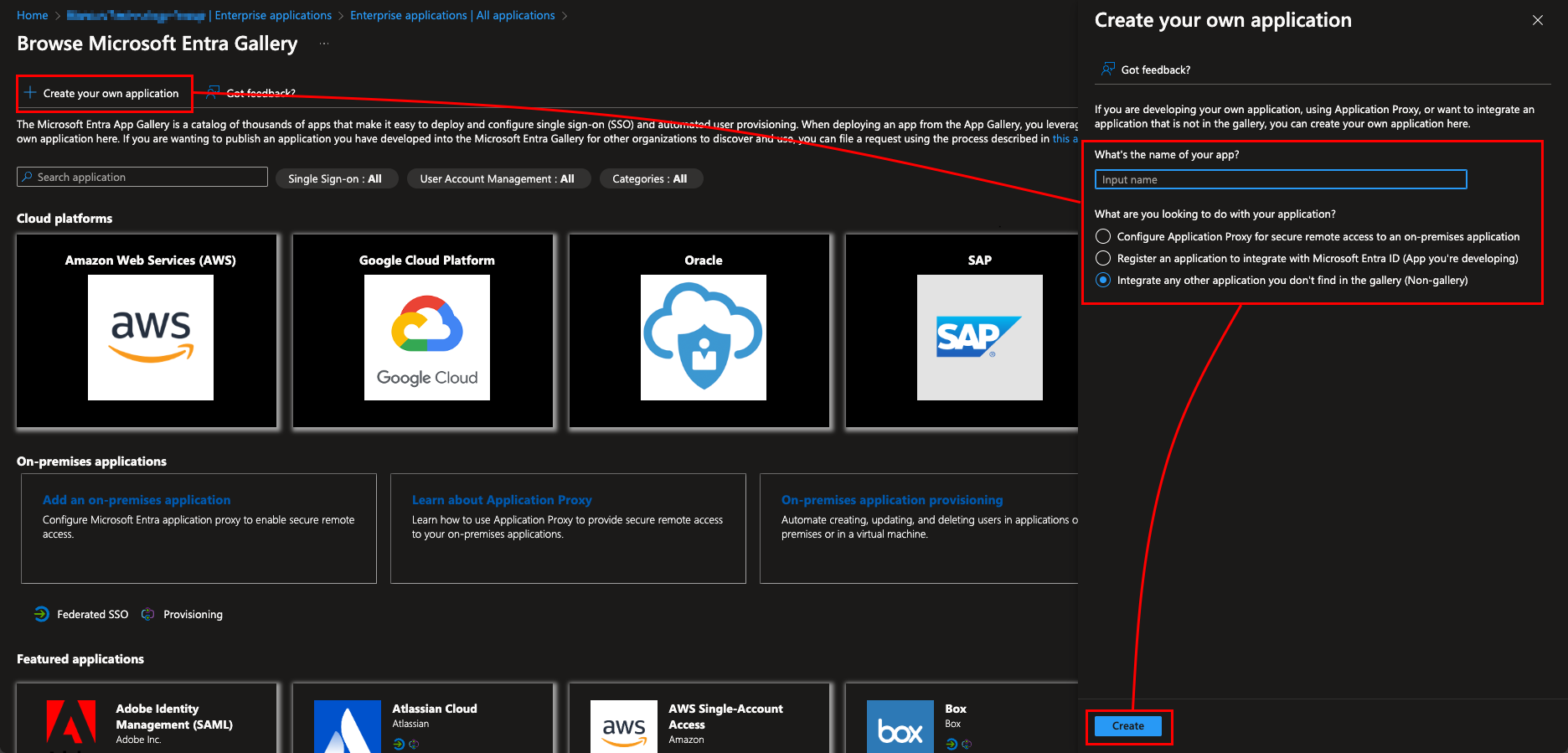
- Create a new enterprise application by opening Entra ID → "Enterprise applications" → "New application".
Then select "Create your own application" and fill in the name of the application. Also make sure to select the "Non-gallery" option under the "What are you looking to do with your application?" section. - Assign corresponding users/groups to the newly created application (this defines the list of users who are allowed to sign in using SSO). Alternatively you can disable the Properties option "Assigment required?" to allow any user in your Entra ID tenant to login using SSO.
- Configure required settings under the "Single sign-on" tab (make sure to select "SAML" as the sign-on method)
- Under the "Basic SAML Configuration" define "Identifier (Entity ID)", "Reply URL (Assertion Consumer Service URL)" and "Sign on URL".
- "Identifier (Entity ID)" corresponds to "Service Provider ID" available in the BMP SSO settings
- "Reply URL (Assertion Consumer Service URL)" and "Sign on URL" both correspond to Single Sign-On URL available in the BMP SSO settings.
- Under "Attributes & Claims" the "name" attribute should be set to "user.displayname" (by default this is set to "user.userprincipalname").
- Acquire "App Federation Metadata Url" which is available under "SAML Certificates" section and copy the URL to BMP SSO settings to the "SAML metadata URL" field.
- Under the "Basic SAML Configuration" define "Identifier (Entity ID)", "Reply URL (Assertion Consumer Service URL)" and "Sign on URL".
Microsoft Entra ID/Azure AD - SSO with OpenID Connect
Follow these steps to set up single sign-on with Azure AD using OpenID Connect.
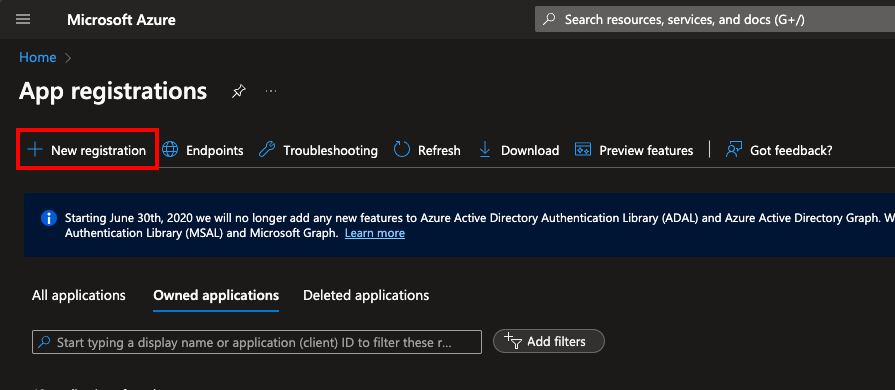
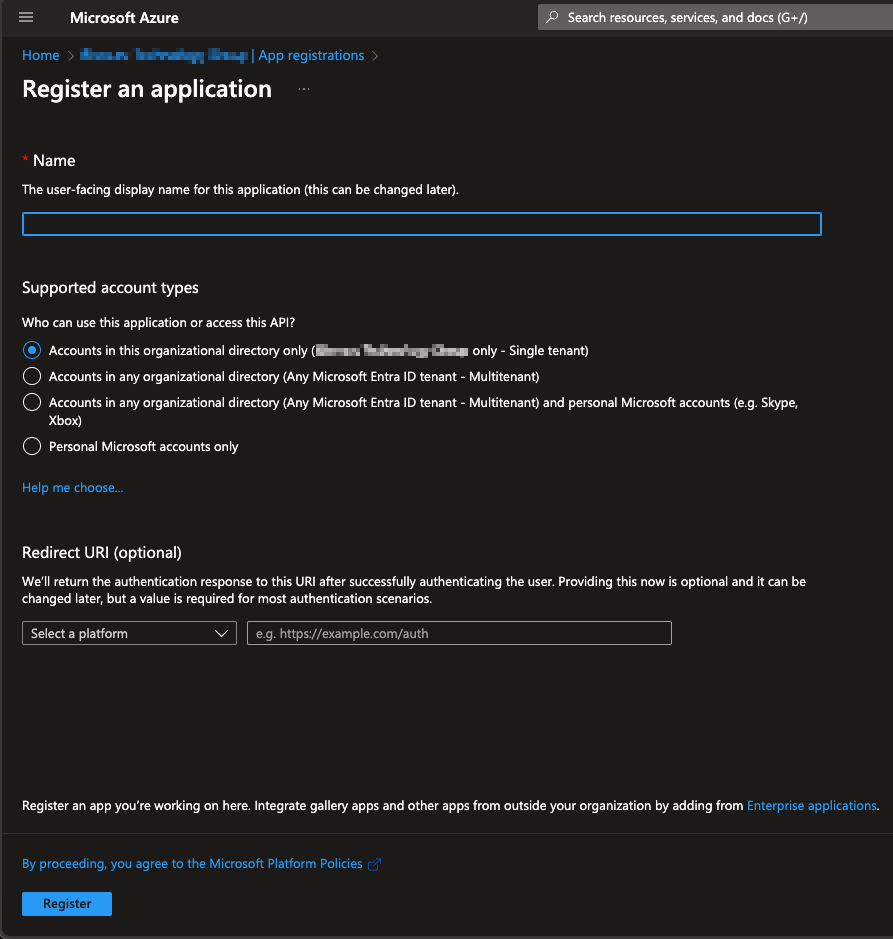
- Register a new application in by navigating to "App registrations" and then selecting "New registration".
Fill in the name and select appropriate account type, in this example single tenant option is selected. Set the "Redirect URI", use the Single Sign-On URL available in BMP SSO settings as the redirect URI. - After registering the app copy "Application (client) ID" from the app to the BMP SSO settings "Client ID" field.
- Navigate to "Certificates & secrets" to generate new client secret by selecting "New client secret" under the "Client secrets" -tab.
- Define description and expiration for the secret and click "Add".
After creating a new secret copy secret's value and enter it as the "Client secret" in BMP SSO settings.
Info Note that the secret value is only shown right after creating a secret. If the value is already hidden and wasn't copied over a new secret needs to be created.
- Navigate to "API permissions" and grant admin consent for the "User.Read" API/Permission. This enables the system to check required user attributes need for the SSO authentication.
- Navigate to "Authentication" and make sure "Redirect URIs" is configured. If this was already configured when creating new app registration, this step can be ignored.
- Use the Single Sign-On URL available in BMP SSO settings as the redirect URI.
- Acquire "Issuer URL" from the "OpenID Connect metadata document".
- Open the document and locate "issuer" field from the document and copy the value to "Issuer URL" field in BMP SSO settings.
Limiting user and group access for the OpenID Connect SSO
When the new application was registered as part of the previous steps, the system should have created an Enterprise Application with the same name automatically. This Enterprise Application can be used to control the list of users and groups who are allowed to use the SSO (similarly as with the SAML).
- Go to "Enterprise Applications" and locate the correct app, it should have the same name as the App registration which was created on the above steps.
- Navigate to "Properties" and set "Assignment required?" to "Yes".
- Navigate to "Users and groups" and define the list of users and/or groups allowed to sign in using SSO.